Fortinet
FCSS_SASE_AD-25
Q1:
How does FortiSASE hide user information when viewing and analyzing logs?
○
A
By tokenization in log data○
B
By masking log data○
C
By compressing log data○
D
By hashing log data
Fortinet
FCSS_SASE_AD-25
Q2:
How do security profile group objects behave when central management is enabled on FortiSASE?
○
A
Objects support two-way synchronization.○
B
Objects created on FortiSASE can be retrieved on FortiManager.○
C
Objects that are only flow-based are supported.○
D
Objects are considered read-only on FortiSASE.
Fortinet
FCSS_SASE_AD-25
Q3:
Refer to the exhibits.
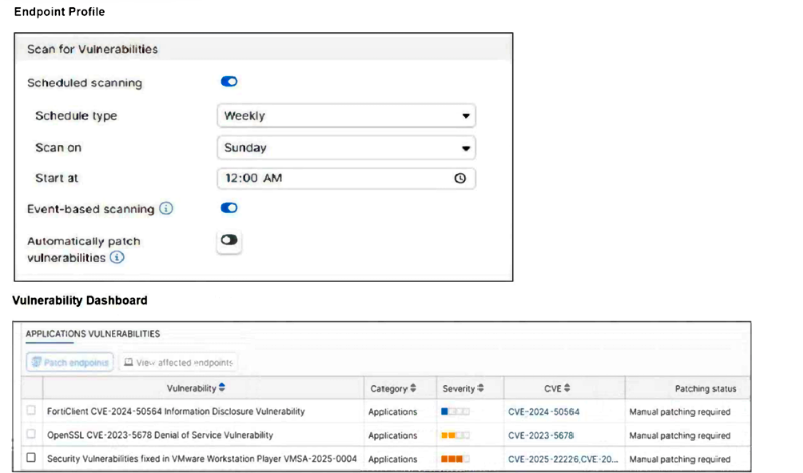
How will the application vulnerabilities be patched, based on the exhibits provided?
○
A
The vulnerability will be patched automatically based on the endpoint profile configuration.○
B
The vulnerability will be patched by installing the patch from the vendor's website.○
C
The end user will patch the vulnerabilities using the FortiClient software.○
D
An administrator will patch the vulnerability remotely using FortiSASE.
Fortinet
FCSS_SASE_AD-25
Q4:
What are two benefits of deploying secure private access with SD-WAN? (Choose two.)
☐
A
a direct access proxy tunnel from FortiClient to the on-premises FortiGate☐
B
ZTNA posture check performed by the hub FortiGate☐
C
support of both TCP and UDP applications☐
D
inline security inspection by FortiSASE
Fortinet
FCSS_SASE_AD-25
Q5:
A company must provide access to a web server through FortiSASE secure private access for contractors.
What is the recommended method to provide access?
○
A
Configure a TCP access proxy forwarding rule and push it to the contractor FortiClient endpoint.○
B
Update the DNS records on the endpoint to access private applications.○
C
Publish the web server URL on a bookmark portal and share it with contractors.○
D
Update the PAC file with the web server URL and share it with contractors.